Domain impersonation takedowns: what works and what doesn't
Understanding the challenge
Domain impersonation is one of those problems that looks simple on the surface but becomes messy very quickly. Someone registers a domain that looks close enough to a real brand to fool people, then uses it to send emails, host fake login pages, or run payment scams. By the time the brand notices, money or credentials have often already moved.
Effectiveness varies by method
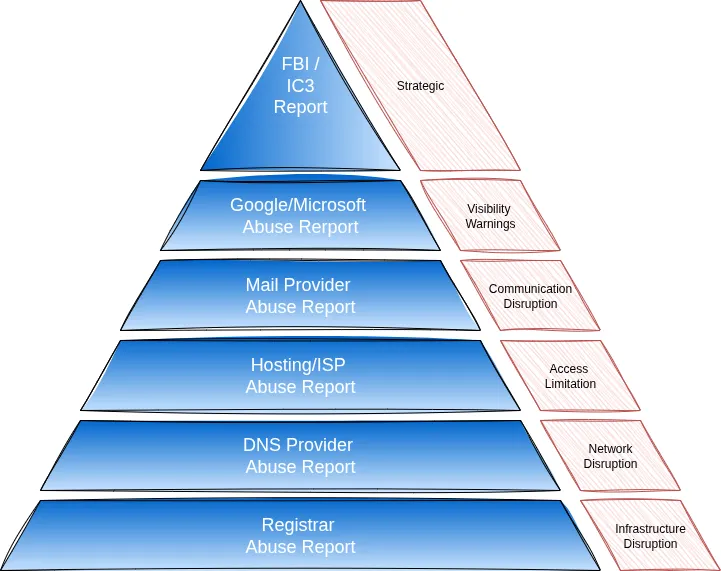
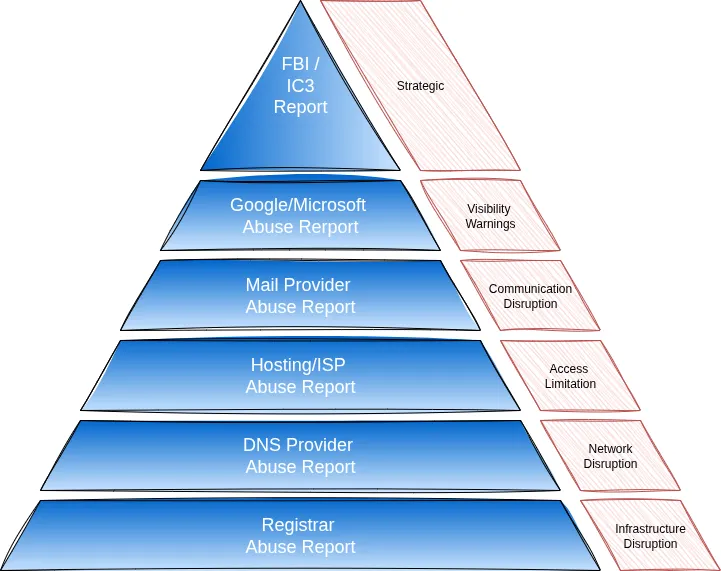
There are several ways to deal with these domains, but they are not equal. Some routes shut the operation down at its root, while others only make it harder for the scammer to keep going. Reporting the domain to the registrar, DNS provider, or hosting company tends to cause the most direct damage. Browser and security reports make the domain harder to use. Law enforcement reports add pressure but rarely stop the scam immediately.
Recommended response order
If the aim is to cause the most harm to the scammer, the order usually looks like this: registrar takedown, DNS provider takedown, hosting or ISP shutdown, Google Safe Browsing, Microsoft unsafe site reporting, mail provider action, and finally law enforcement reporting. In real incidents, the most sensible move is to push on several fronts at once, since scammers often rely on speed and volume to stay ahead.
Step 1 – Triage and evidence grab
Take screenshots of every important page:
- Home page.
- Login and payment pages.
- "Contact us" pages with fake phone or chat details.
Save raw emails that point to the domain:
- Export as .eml if possible.
- Copy full headers.
Run basic lookups:
- WHOIS – note registrar and registrant data (if visible).
- DNS – write down A/AAAA (IP), NS, MX, and name of DNS provider.
Confirm your brand link:
- Your real domain and URL of the genuine portal or login page.
- Trademark number or registration details, if handy.
Drop all this into a single incident doc or ticket so you never have to repeat the collection work.
Step 2 – Hit the domain's "life support" first
Registrar abuse report
This is the company that sold the domain to the scammer. Think GoDaddy, Namecheap, NameSilo, Gandi, and others.
If the registrar suspends the domain, the scam dies immediately. Site gone. Emails stop. Damage halted.
Use the registrar's abuse form or abuse@ email from WHOIS.
Include:
- Domain.
- Summary of impersonation.
- Screenshots.
- Evidence of your rights (real domain, trademark, registration).
- Any active harm (lost money, harvested credentials).
Keep it factual and short, but with enough detail that a human can see the fraud straight away.
DNS provider abuse report
Sometimes the registrar moves slow. The DNS provider controls where the domain points. Think Cloudflare, AWS Route53, Akamai.
If they suspend DNS, the site stops resolving.
If a third-party DNS service is used, submit a separate report.
- Provide domain, screenshots, and evidence that it hosts a phishing site.
- Mention that the domain mimics your brand and is collecting credentials.
Hosting / ISP abuse report
Take the IP from DNS and look up the hosting company or network.
- Use their abuse contact (often abuse@ or a form).
- Send URL list, IP address, and screenshots.
- Mention if you know of real victims or money loss.
Doing these three together gives you three possible ways to cut the site off from the internet. If even one bites, the scammer's day gets worse.
Step 3 – Flag the domain with security providers
Google Safe Browsing "Badware / Phishing"
- Submit each unique phishing URL.
- Attach screenshots and a short description of the data being stolen.
- Mention your real domain that is being copied.
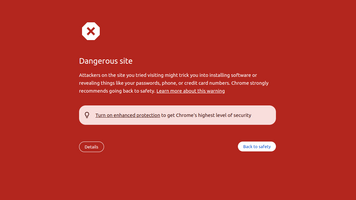
Microsoft "Report unsafe site"
- Use the linked form.
- Again, add URLs, screenshots, and a brief summary of the harm.
These reports do not always kill the site, but they make it much harder for victims to reach it without big browser warnings.
Step 4 – Cut off scammer email
Report to the mail provider in the MX record
From your DNS lookup, grab the MX host(s).
Look up who runs that mail platform (large providers are easy to recognise).
Send them:
- Copies of phishing messages with full headers.
- Addresses used (billing@fakebrand.com, etc.).
- Evidence that these addresses impersonate your brand or staff.
Ask them to:
- Suspend the abusive mailbox or tenant.
- Block further outbound mail of that type if they see more.
This step is especially helpful when the scammer is still live but your main aim is to protect less technical users who might click anything that turns up in their inbox.
Step 5 – Law-enforcement and internal follow-up
Submit an FBI / law-enforcement report
If the campaign touches US persons or banks, send a report to IC3 or the relevant portal.
Include:
- Domain details.
- Screenshots.
- Bank accounts or payment routes that were used.
- Money lost (if any).
If you are outside the US, also report to your own country's cybercrime unit.
This step is not about speed. It is about stacking the deck against repeat offenders.
Internal clean-up
- Notify your own staff (especially helpdesk and finance) about the fake domain.
- Add banner text or an internal note: "We will never send you to contoso-login.com," etc.
- If any customers were targeted, send a short alert with screenshots of the fake site so they can recognise it.
The response pyramid
In a domain impersonation response, the instinct might be to strike at the top first, but in practice the most effective approach is to work from the base upward, moving layer by layer.
Where monids.com fits into this story
Now imagine you don't want to play detective, gather screenshots, chase registrars, and fill out five different abuse forms.
That's where monids.com steps in.
Here's how it works.
Do you handle Domain Takedowns?
Yes.
When you spot a threat, you can request a Domain Takedown or have it handled proactively on your behalf.
Monids.com supports customers through the full takedown process. From gathering proof to coordinating with registrars, DNS providers, hosting companies, and email services.
You're not left wondering who to contact or how to word the report.
We stay on it until the domain is suspended or neutralised.