How Attackers Use Lookalike Domains Against You (And How to Get Ahead of Them)
Every phishing campaign starts the same way. Before there's a malicious email, before anyone clicks anything, an attacker registered a domain. That's the part most security programs never see coming.
The attack itself gets all the attention. Someone clicked a fake Wells Fargo link, someone got a Microsoft Teams installer with a trojan inside. By the time that happens, the domain has already done its job. The question worth asking is: could you have spotted that domain before it was used?
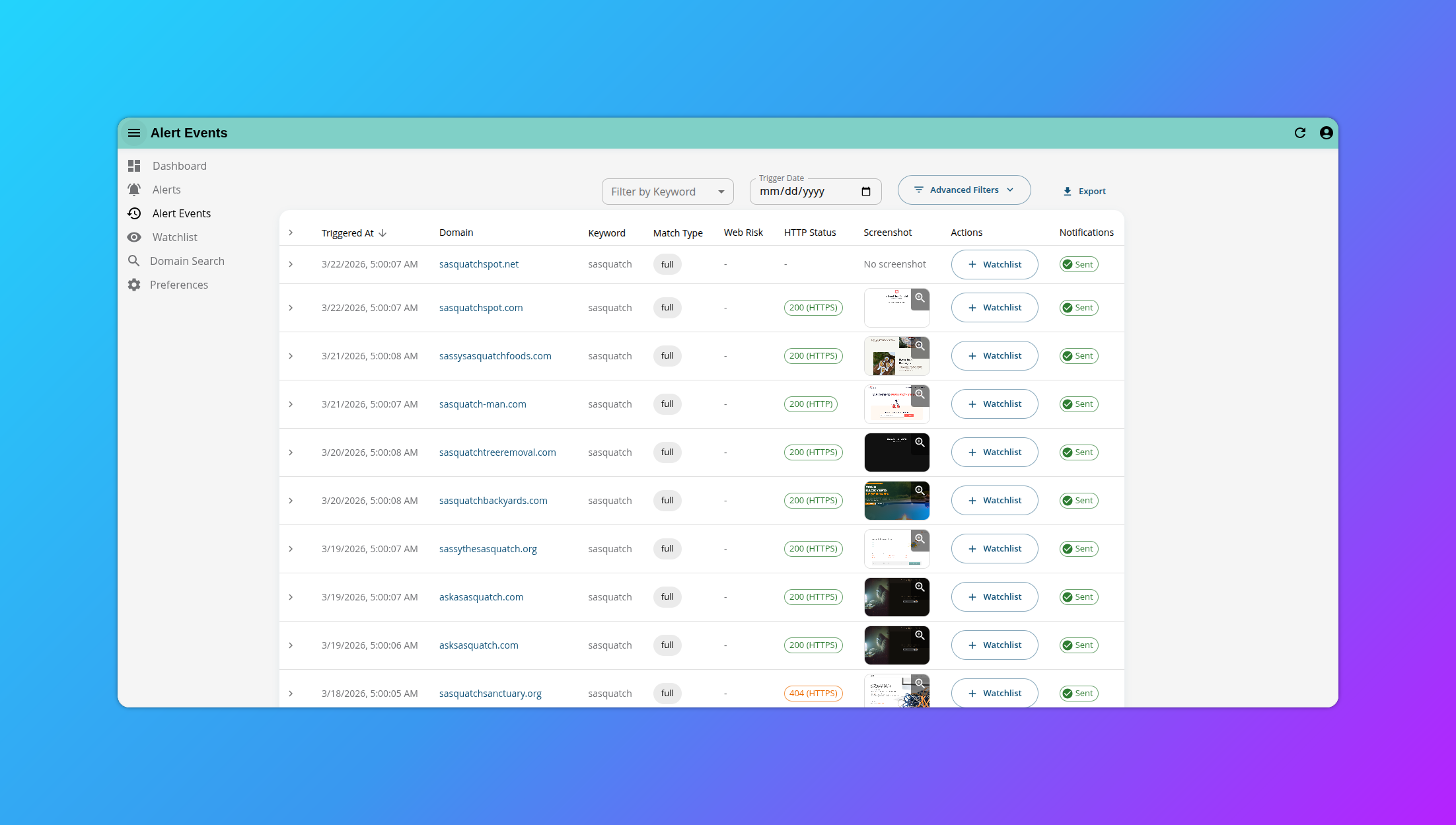
Monids dashboard: newly discovered domains for a monitored keyword, with timestamps showing detection within hours of registration.
How Attackers Actually Set This Up
Attackers running phishing or brand impersonation campaigns follow a pretty consistent playbook. They pick a target, come up with a name that looks close enough to be convincing ("microsoft-msteams.com" instead of "microsoft.com"), register the domain, get it live with hosting, and then run whatever fake page or payload they're pushing.
The whole sequence, domain registration to active attack, can happen in hours. Sometimes less. Most of the time, detection happens at the very end of that chain, when someone's already been hit and the domain finally shows up in a threat intel feed.
Here's the thing: domains can't be invisible. If they were, they wouldn't work. Every domain leaves a trail the moment it's registered, and that trail fills in as it gets configured for hosting. That trail is there to be read; you just need to be reading it early enough.
Legitimate: microsoft.com
Lookalike: microsoft-msteams.com — one extra segment, enough to look legitimate at a glance
Monids feature: Monids scans 1,570+ TLDs daily for newly registered domains and surfaces any that match your brand keywords, including fuzzy variants like typosquatting patterns. You see the domain often within hours of registration, before most threat intel feeds would ever pick it up.
The Problem with Waiting
Blocklists and threat intel feeds are valuable, but they're almost always reactive. By the time a domain appears in one, it's usually been active long enough to do damage. You're essentially catching up.
This isn't anyone's failure; it's just how the process works when detection depends on observing harm first. The pattern of "register, get it live, attack, get detected" means defenders are always behind unless they're watching for domains before they get used.
Finding something early changes what you can do. If you see a lookalike domain surface right after registration, you have options: watch it, check whether it's being set up with infrastructure, decide whether to block it before the campaign starts. The domain exists, but nothing's been sent yet. That window is where brand protection actually has room to work.
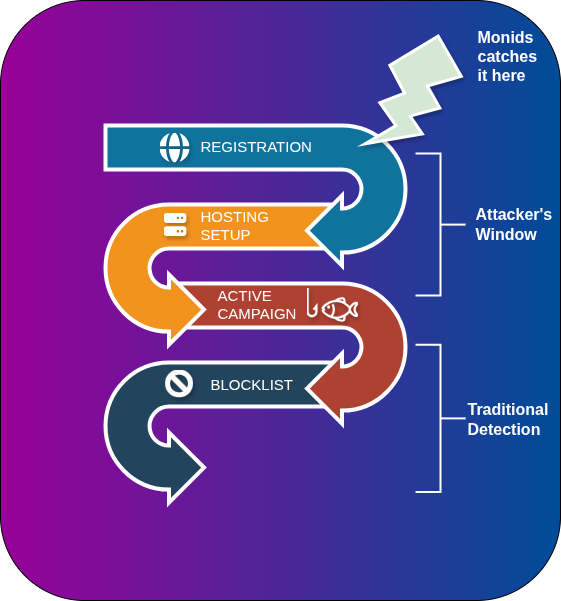
Attack lifecycle: Registration → Hosting setup → Active campaign → Blocklist detection. Monids detection happens at the first step.
What Makes Monitoring Hard in Practice
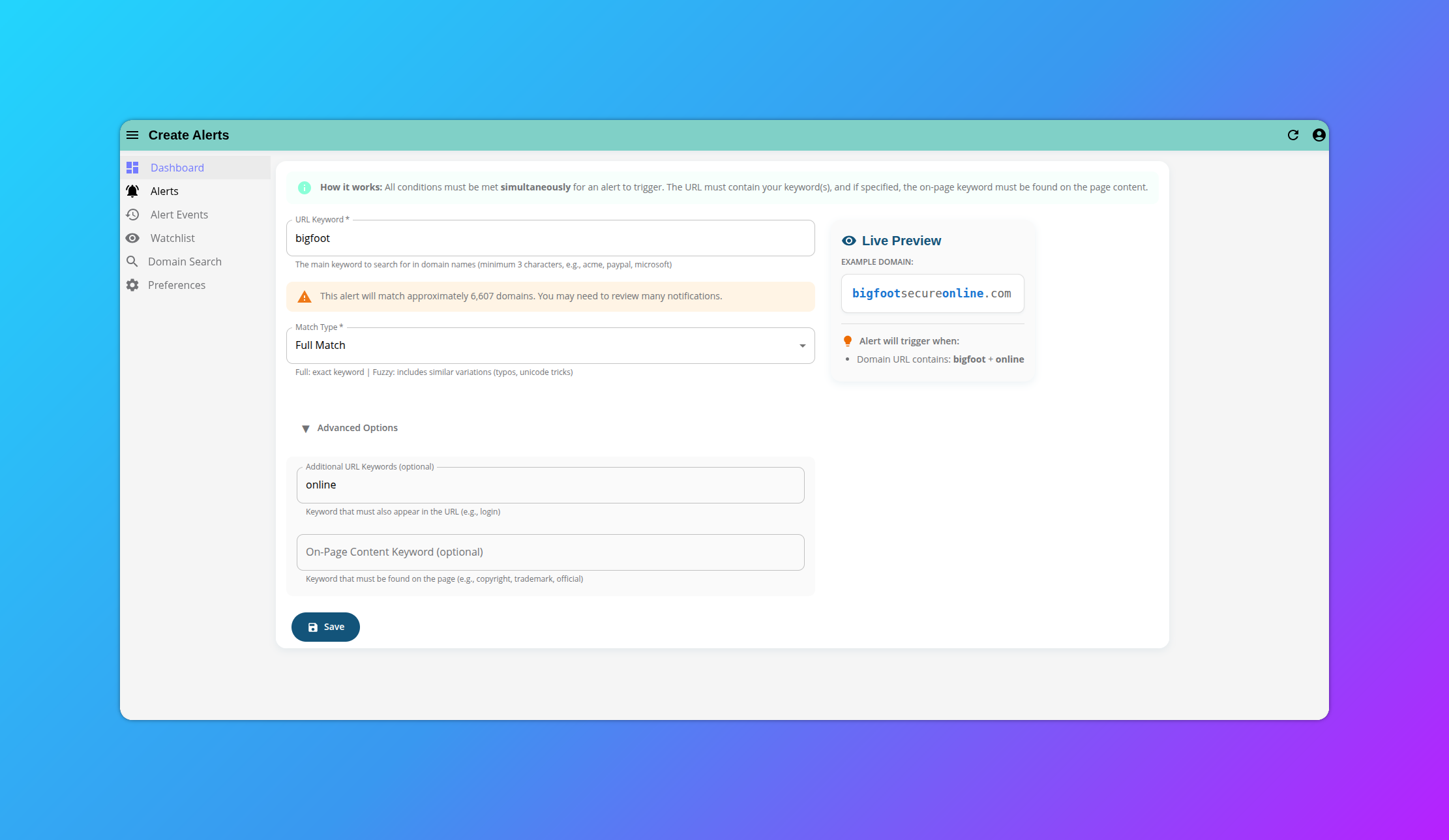
It depends on your brand and how you've set up your monitoring. Broad search terms catch a lot, but too many results and you can't work through them. A company monitoring "apple" will surface pineapple domains along with genuine impersonation attempts. That's noise, and too much noise means the whole exercise breaks down.
On the other end, overly specific monitors can give you false confidence. You're watching for "yourcompanyname.com" variations but missing "yourcompany-login.net" because you didn't account for that pattern.
The practical challenge for most security teams is tuning this middle ground: specific enough to be useful, broad enough to catch what you didn't anticipate. Getting that signal-to-noise ratio right matters because if your team is drowning in false positives, they'll stop trusting the alerts.
Monids search results for a keyword monitor, with include/exclude filters to tune signal-to-noise ratio.
Monids feature: When setting up a monitor in Monids, you get a preview of how many domains your keyword has historically matched per day. That gives you a read on volume before you commit, so you can tune the term to get a manageable, useful signal rather than an overwhelming one.
Triaging at Scale
For larger organizations, volume is real. It's not unusual to see dozens or hundreds of suspicious domains per day matching your brand terms across 1,500+ TLDs. You can't investigate them all with equal depth.
Some of those domains will sit dormant. Speculative registrations, abandoned campaigns, or someone who just wanted the name. Others will quickly acquire DNS records, hosting, SSL certificates, signs that someone is building something.
Risk signals matter here. DNS activity, hosting configuration, passive DNS traffic, on-page content; these tell you whether a domain is just sitting there or being actively set up. A domain with matching page content, fake login elements, or your company's branding copied onto it is a very different situation from one that resolves to a parked page.
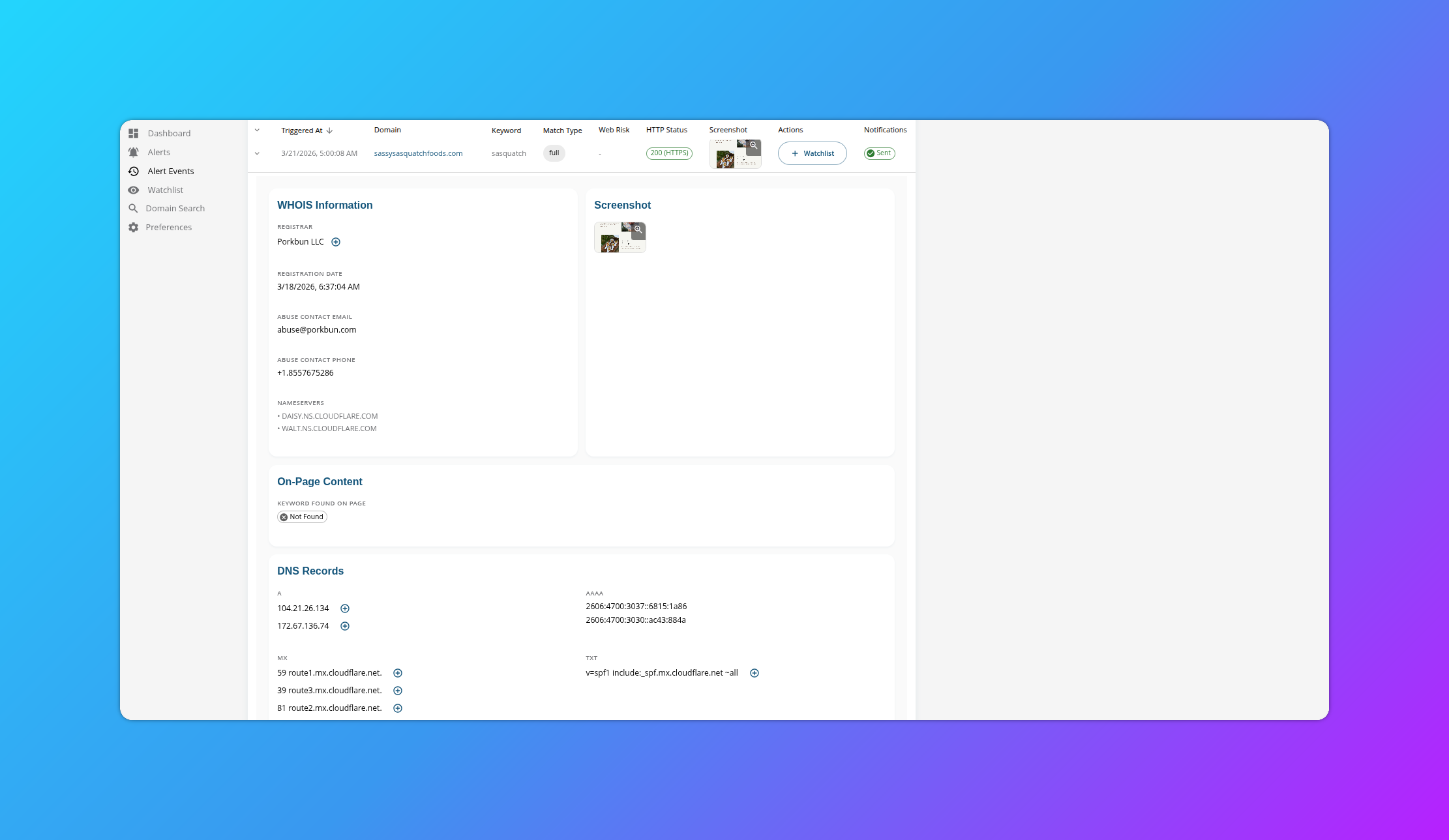
Monids domain detail: WHOIS records, DNS data, registrar info, and an automated page screenshot side by side.
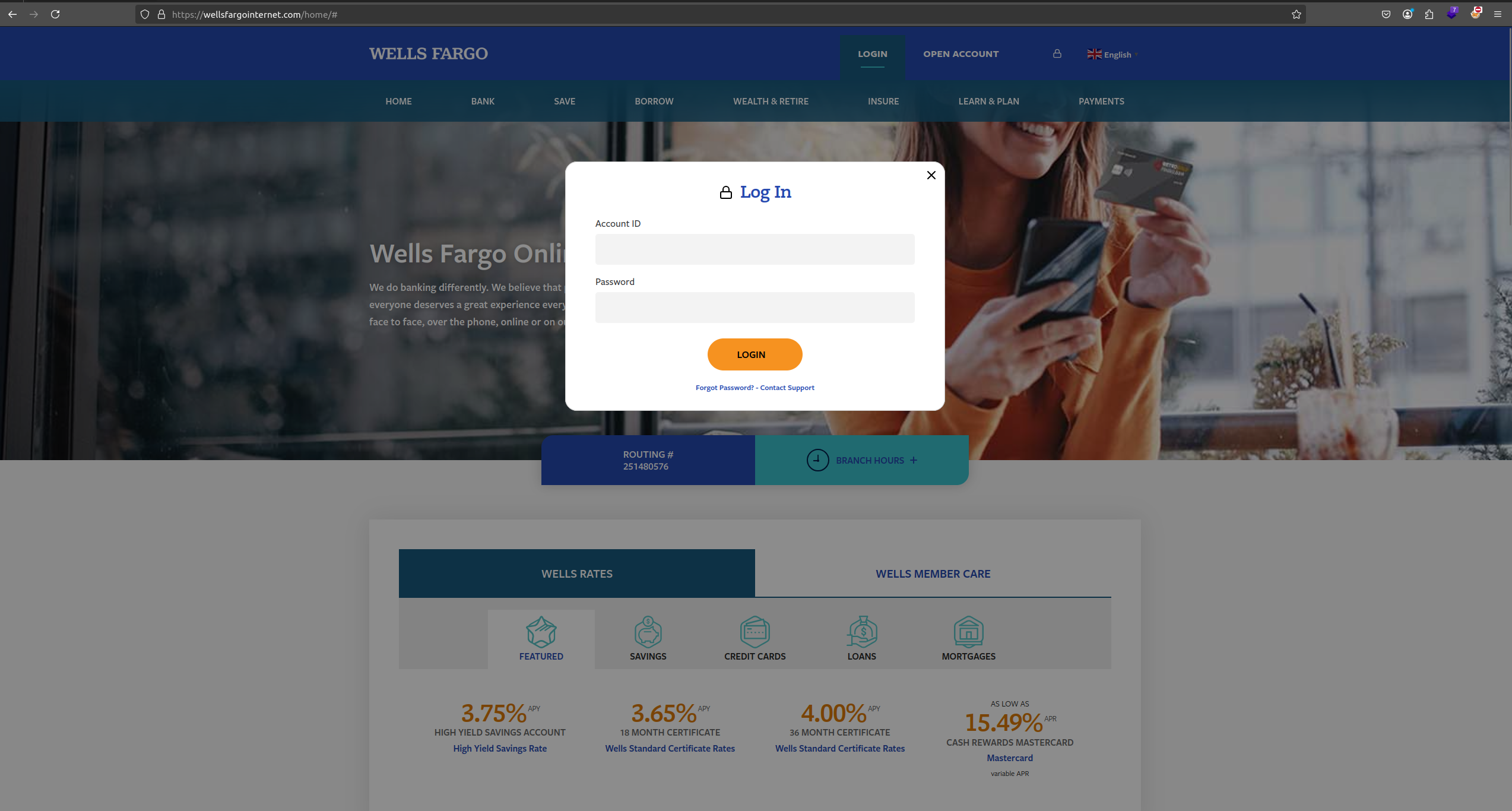
Example of an active brand impersonation page captured by Monids. A domain like this, resolved and serving content, is a very different risk than a parked domain.
Monids feature: Each flagged domain in Monids comes with enrichment data: WHOIS records, DNS records, registrar details, and automated page screenshots. You can see what's actually on a domain without visiting it yourself, which means triage is faster and you don't need to open a browser to a potentially malicious site.
The Action Phase Doesn't Have to Be Complicated
Once you've identified something genuinely malicious, the options are roughly: internal blocking, escalation to registrars or hosting providers, reporting to browser vendors, or in serious cases, law enforcement. Each one works differently and moves at its own pace.
Registrar abuse reports tend to be the most direct route to takedown. Browser vendor reporting (Google Safe Browsing, Microsoft's unsafe site process) is useful for limiting reach even before a domain is taken down. Internal blocking (adding a domain to your DNS resolver or firewall) is something you can do immediately without waiting on anyone else.
None of these are guaranteed to be fast, and takedowns often take longer than you'd like. The earlier you catch a domain in its lifecycle, the more time you have to work through those channels before it causes harm.
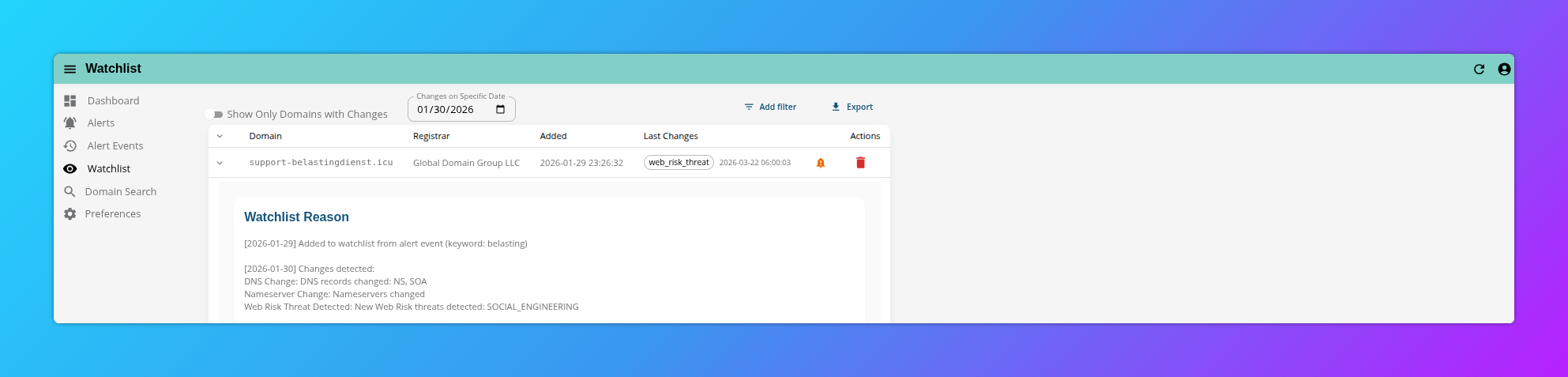
Monids watchlist: a previously dormant domain just acquired hosting and DNS records, a signal worth acting on.
Monids feature: Domains you're watching in Monids get tracked over time. When something changes (new DNS records, hosting stood up, on-page content updated), you get notified. That means you're not checking manually, and you don't miss the moment a dormant domain becomes active.
Why This Is a Brand Problem, Not Just a Security Problem
Impersonation domains affect more than just your security posture. A fake login page using your brand erodes customer trust even if your systems were never breached. Fraudulent emails that look like they came from your domain damage your reputation with the people receiving them. In some cases, users can't tell the difference between a real and fake site until they've already entered their credentials.
Brand teams, legal teams, and security teams all care about this problem from different angles. The monitoring and triage workflows look similar regardless of which team is running them.
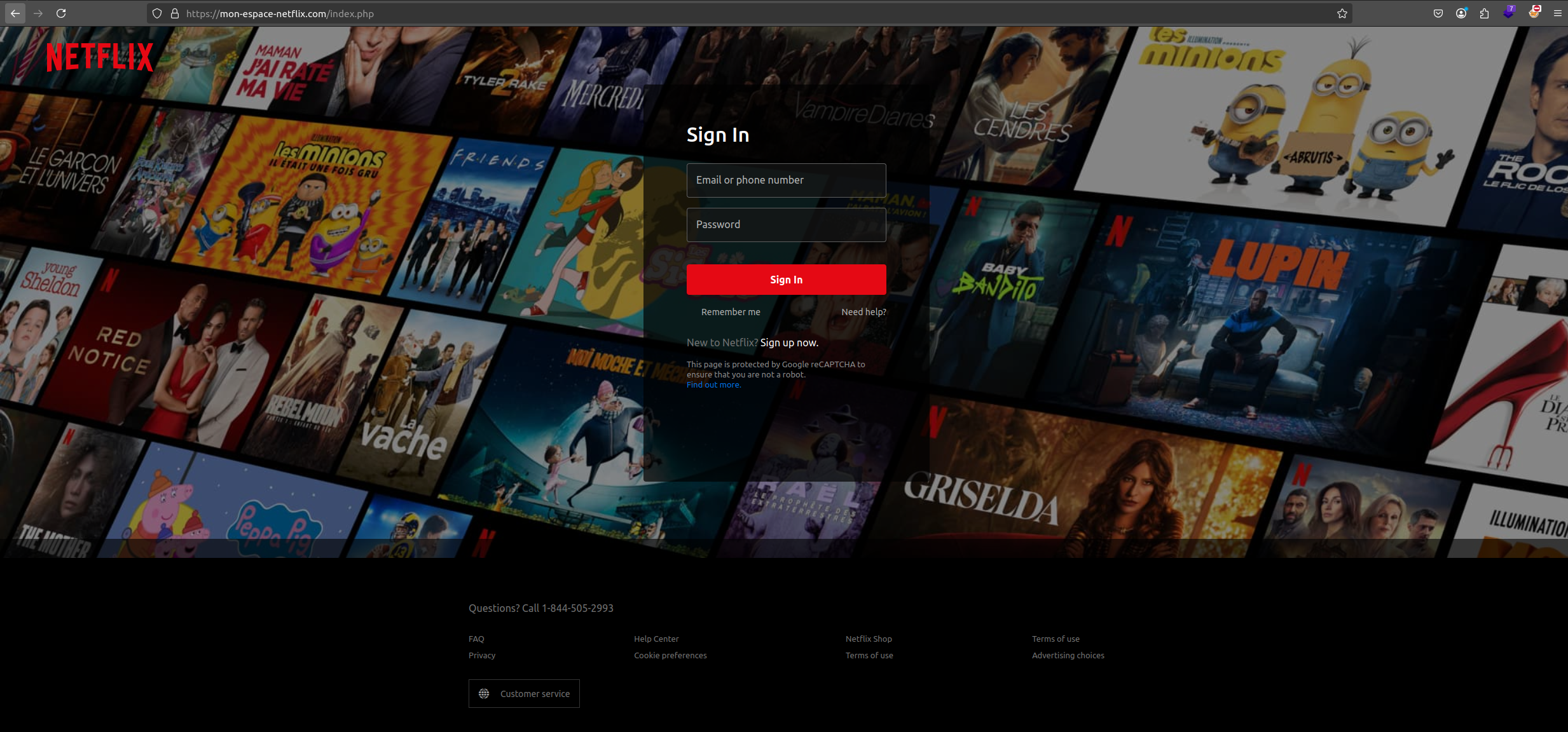
A convincing fake login page. The domain looks close enough to the real thing that users often don't notice until it's too late.
Getting Ahead
The reality is that you probably have lookalike domains out there right now. Most organizations with any recognizable name do. The question isn't whether they exist; it's whether you're finding them before attackers use them, and whether you have a process for doing something about the ones that matter.
That gap between registration and weaponization is where the opportunity is. It's not a wide window, but it's there. Monitoring for new domains that match your brand, enriching them with context, and triaging the ones that show active infrastructure is about as close to proactive as this kind of threat allows.
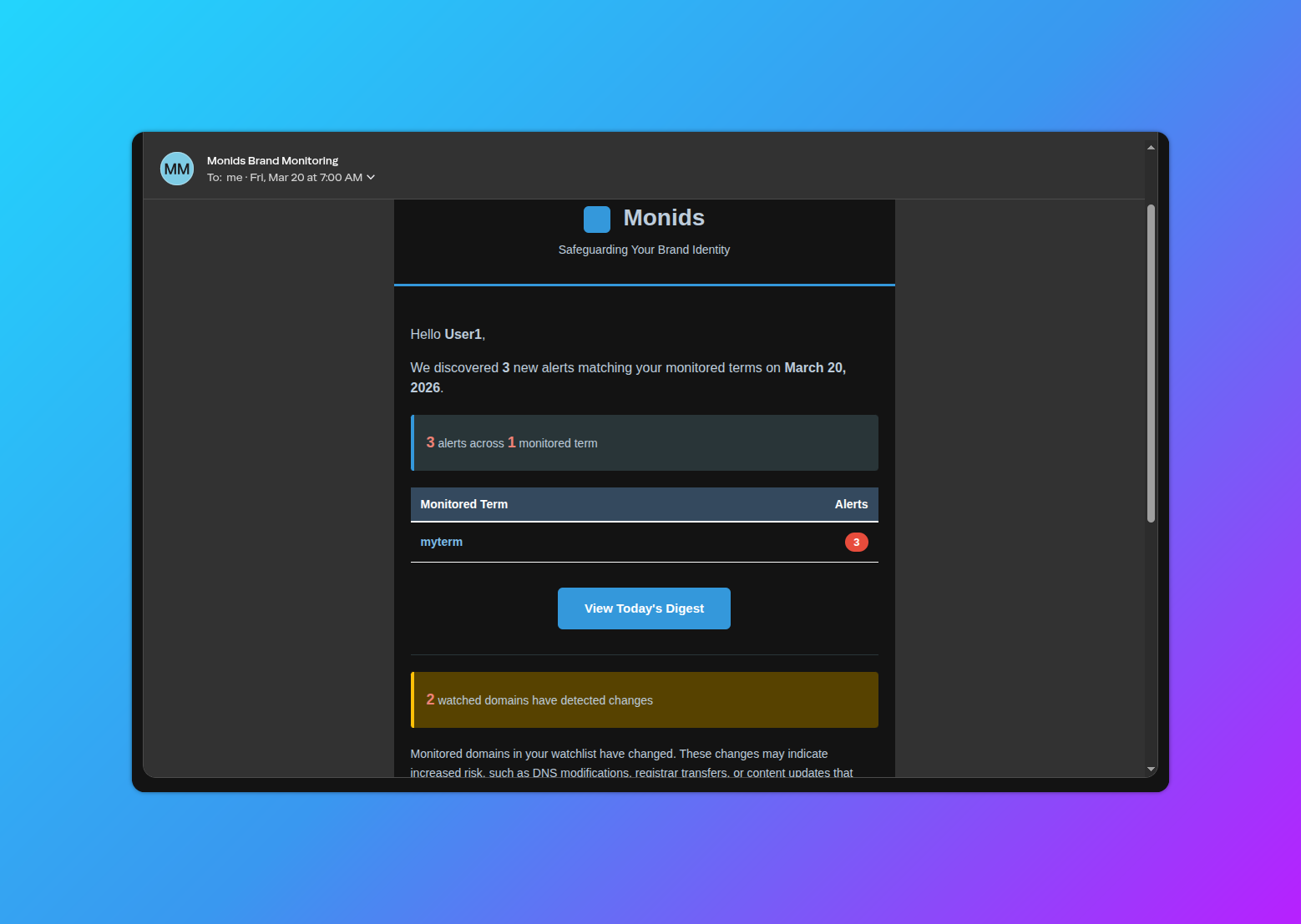
A Monids alert notification with key domain details inline, showing the full workflow from detection to your inbox or Slack.
Monids feature: Monids is built around exactly this workflow. Set up keyword monitors, get alerted when new matching domains appear, review enrichment data and screenshots in context, and act on the ones that look live. You can also connect alerts to Slack, Splunk, or your own systems via the REST API so the signal lands wherever your team already works.